In today’s episode of Undisclosed, Postconviction Relief Part 5: Closing Thoughts, we discussed in greater detail how the cellphone records at Adnan’s trial were not the authenticated copy of records that they were purported to be. Although Exhibit 31 — a.k.a. the Frankenzibit — had been presented by the prosecutors as an authenticated copy of AT&T’s business records, the documents that were authenticated by AT&T had been substituted for a different and unauthenticated copy of the records, from which all fax information had been removed.
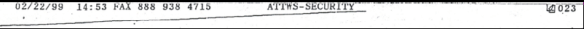
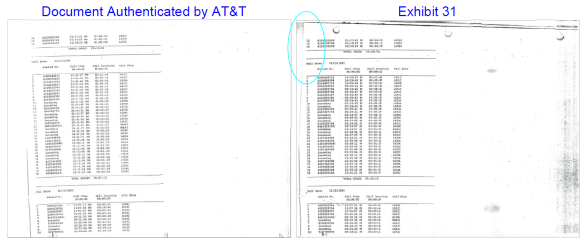
You can see these differences four yourself by comparing Urick’s fax to AT&T requesting authentication of the State’s copies of the cellphone records, and Exhibit 31 as it was admitted at trial. To show the differences between the two documents, I’ve provided below a side-by-side comparison of each page. (Note that the substantive records begin at Page 2 of Exhibit 31; the first page is the affidavit from AT&T’s custodian.)
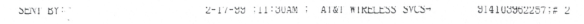
The second page of Exhibit 31 is the subscriber information sheet from AT&T’s 2/17 fax. In the document Urick sent to AT&T for authentication, the top line reads: “SENT BY: 2-17-99 ; 11:30am ; AT&T WIRELESS SVCS- 914103962257 ; #2.”
In Exhibit 31, the top line has been chopped off, and the entire page has been shifted upwards — including the hole punches on the left-hand side, which are now noticeably higher than those on the authenticated copy.
The third page of Exhibit 31 is the last page AT&T’s 2/22 fax, containing part of the phone records for January 12, as well as blank entries for phone records from January 9 – 11 (prior to the phone’s activiation). On the left side of the document faxed by Urick to AT&T, the edge of the original fax header is visible, while it has been removed from the copy submitted as Exhibit 31.
The fourth page of Exhibit 31 is the second to last page of AT&T’s 2/22 fax, containing part of the January 14 records, all of the January 13 records, and the beginning of the January 12 records. In Urick’s fax to AT&T, the fax header information has already been almost entirely cut off (although it remains present in the prosecution’s other copy of the January 13 records from the 2/22 fax). However, because the original fax from AT&T was slightly askew, the border of the fax header information is not parallel with the page’s text, and runs off at a ~15° angle. In the corresponding page from Exhibit 31, this has been corrected with the help of a paper guillotine; however, because of the angle required to even up the page, the sheet of paper was no longer a rectangle, and copies made from the cut sheet show where fax header side was cut off (circled in blue, top right of image).
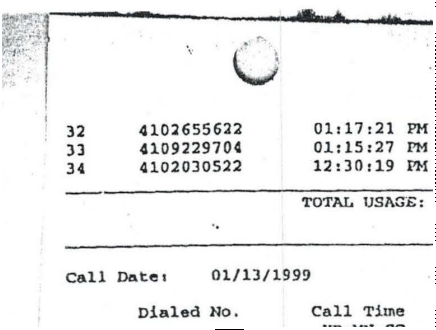
The shadow from where the paper is lying on the copier glass is visible, demonstrating that the corner is not at a 90° angle.
The fifth page of Exhibit 31 is the third-to-last page of AT&T’s 2/22 fax, containing the beginning of the January 14th records and part of the January 15th records. In Urick’s fax to AT&T, a recognizable portion of the fax header information line is present:

However, in the document submitted as Exhibit 31, the fax header has been removed, and the entire page has been repositioned so that the text is angled correctly.
To break down how this happened, and why this switch went unnoticed at trial, it helps to review a timeline of events resulting in the creation of Exhibit 31:
- On February 17th and 22nd, during the investigation into Adnan, AT&T faxed copies of Adnan’s phone records to the BPD (the 2/17 and 2/22 faxes, respectively). These copies had fax header information prominently displayed on all pages. It looked like this:
- Copies of these phone records were provided to the prosecution in preparation for Adnan’s October 13th trial date.
- On October 8, 1999, Urick faxed four pages of phone records (one from the 2/17 fax, three from the 2/22 fax) to AT&T’s custodian of records, with a letter stating, “Pursuant to your telephone conversation this date, I am faxing you four pages of AT&T Wireless billing records that we obtained per a subpoena. I would appreciate it if you could return the records to me as certified business records.”
- The cellphone records faxed to AT&T had the fax header partially removed, although the header remained fully or partially visible on three of the four pages.
- AT&T’s records custodian reviewed the cellphone records sent by the prosecution, and on October 12th the custodian provided a sworn affidavit stating that “The attached copies of billing records are maintained by AT&T in the ordinary course of business.” The affidavit and records were then sent back to the prosecution for use at trial.
- The prosecution discarded the certified copies of the phone records that it received back from AT&T, but kept the custodian’s sworn affidavit.
- Using its own copies of the phone records, the prosecution prepared a new set of the four-page phone records, from which all traces of fax header information had been excised.
- The affidavit from AT&T’s custodian was then reattached to the prosecution-constructed version of the phone records, and the new records — which had not been reviewed or certified by AT&T — were submitted as certified business records at Adnan’s trial.
In switching an authenticated copy of the phone records for an unauthenticated copy, the prosecution may very well have been motivated by expediency rather than strategy. After all, by that point, the documents would have been a fax of a fax, and possibly a fax of a fax of a fax. He may have decided that the certified business records sent back by AT&T were too messy, and decided to substitute the authenticated records for a “cleaned up” version, one which had been snipped and rotated to make it more professional in appearance.
But the prosecution’s motives in making the switch are irrelevant. An inadvertent failure to disclose exculpatory information has the same constitutional effect as a deliberate failure. Here, regardless of motive, the result was the same: although the genuine certified business records had information which plainly identified them as copies of a faxed document, the counterfeit version did not. A reasonable attorney reviewing Exhibit 31 — such as, say, the Deputy Attorney General of Maryland — could very reasonably conclude that,
“Indeed, the ‘Subscriber Activity’ reports [sent by AT&T] were neither identified as exhibits nor admitted into evidence. What was admitted into evidence were cellphone records accompanied by a certification of authenticity, signed by an AT&T security analyst, and relied upon by the State’s expert who himself was employed by AT&T as a radio frequency engineer.”
However, contrary to the State’s claims in its recent briefing before the trial court, what was admitted into evidence (1) was a subscriber activity report, and (2) was not a certified business record authenticated by AT&T, but instead a different copy of the phone records that was missing information present in the genuine copy. This isn’t just a case questionable corner cutting by the prosecution that has no practical significance, however. If the instruction sheet is determined to be material and exculpatory evidence by the court, this was a Brady violation. Even had Gutierrez known that AT&T sent the instruction sheet along with all of the billing records that it faxed over — which she didn’t, because the prosecution did not disclose those records to her — Gutierrez still had no reasonable way of knowing that Exhibit 31 was itself a document faxed to BPD by AT&T, to which the instruction sheet applied. The fax headers identifying the origins of Exhibit 31, and directly linking the records to the instruction sheet, had been eliminated, even though that information was present in the genuine copy of the records authenticated by AT&T.
-Susan



You continue to amaze snd astound me, Ms.Simpson! The clarity with which you present the FACTS had to embarrass the prosecution past and present. There is some measure of satisfaction in that I am sure. I am glad to have been able to understand most of what both you and Colin have presented regarding rules of evidence as well as the evidence itself. This is due in no small way to you both! You are much appreciated! I anxiously await a positive outcome for Adnan.
Susan,
I admire you for your careful examination of all of these details about the phone records. It’s such a complex but critical issue in this case! You have made the issue understandable for your listeners. Thank you.
There’s an art to every profession and you ( along with Rabia and Colin) have showed us all that you know how to practice the art of the law with intelligence, practicality, careful ctriticism, empathy, and care.
I hope we all don’t have to wait to wait too long until the judge renders his decision. Although it seems patently obvious to me that Adnan isn’t guilty of Hae Min Lee’s murder, I also realize that the judge’s decision must be based on factors that are narrowly defined. I hope those factors tip in Adnan’s favor.
I also sincerely hope that Hae’s killer can be found and brought to justice. Her family deserves to have resolution, and Adnan deserves to be released from the cloud of suspicion.
THANK YOU! For putting your heart and soul into finding the truth.
Best,
Rebecca
You are amazing!!!
Sent from my iPad
>
I think it is probably also important to note (for those under the age of 30) that back in 1999/2000, unlike today, fax transmissions were a standard way of handling communications and they always were transmitted with a cover sheet identifying, at least, the sender’s and the recipient’s contact information, and often a note of explanation. As such, if Gutierrez had seen any indication that the Exhibit originated as a fax, the first reasonable question would have been, “where’s the cover sheet?” She was not given that opportunity in this instance due to Urick’s removal of the “fax thingies” (as you called them in the podcast, Susan). 🙂
When I was in VA, we still did service of discovery and other filings by fax, and the fax cover was always the first page of the filing in my binders. Knowing who sent a fax and when sometimes turned out to be important.
Like you said, perhaps if she’d seen the true document, top line thingies and all, she’d have paused long enough to ask the right questions before agreeing to a stipulation. Or, well, maybe not Gutierrez then, but a competent attorney.
I struggle to find a good word to use here, so I’ll just go with “content,” and by that, I mean the actual call records…
Was any “content” different between the authenticated fax and what was used as Exhibit 31? Or is it only fax headings that have been removed?
What I’m getting at is whether or not the prosecution was actually trying to manipulate content, and thus potentially there is something related to Adnan’s actual innocence/guilt, or if we’re talking about more of a technicality related to Adnan’s legal innocence/guilt.
The screenshots are kinda hard to read, but to me, it looks more like the latter than the former.
My blog’s format doesn’t allow display of the full sized images, but you can view the linked documents to see them in full.
And I have no idea what the prosecution was trying to do. All I can see is the result, which is that information that was an important clue to the origins of Exhibit 31 — and the relevance of the instruction sheet stating that incoming calls “will NOT be considered reliable information for location” — was present in the authenticated records from AT&T, and not present in the unauthenticated document submitted by the prosecution.
It’s just a technicality in the same way due process is a just a technicality.
I didn’t say “just a technicality.” Technicalities are extremely important.
From Webster:
What I was wondering is if the fax headers were a technicality, or if the headers actually said something about the content of the documents that was lost without them.
Hence, my question. Is this more of a “small detail in a rule, law, etc.? Or something that is understood by experts by not by other people”? I didn’t mean “technicality” in any negative way. It was an honest question.
Well done on the comparisons. I’m curious if (back then) a fax cover sheet was considered part of the evidence itself by the court? I understand the importance of the message it contained in this particular case, but was there an obligation for the prosecution to keep it as part of the chain of evidence in general? Consider if the phone records were mailed in, is the prosecution required to keep the envelope in case the post date on the stamp is important, where it was mailed from, whose fingerprints were on the envelope, etc.? More of a curiosity here.
Whether the message on the cover sheet is exculpatory or not I believe is unclear. ‘NOT considered reliable’ does not equal ‘incorrect’, meaning the lack of reliable information in those calls does not exonerate Adnan. This is where CG made a big mistake IMO – she should have attacked the phone records more aggressively in the trial. If whomever the fax person was at AT&T knew about the unreliability of location for incoming calls, certainly CG should have been able to find an expert with a similar opinion.
Maybe this is addressed somewhere else, but if there were faxes on 2-17 and 2-22, shouldn’t there be two fax cover sheets?
Hey Susan, the vitriol has really increased lately. I saw this
and people were saying the schools Thiru got into wouldn’t let you wash their floors.
They used to leave you alone, do you think it’s because of Asia’s book?
**feel free to take the link out if you don’t want others to see it or it hurts your feelings, I just thought you should know.
That’s hilarious. Thanks for sharing — I’ll leave it up so everyone else can appreciate it too.
Ah, the last refuge of the truly desperate: argumentum ad college rankings.
When they have nothing substantive to say to refute evidence against their position, they simply dismiss the evidence at hand and resort to name-calling and creating childish memes.
There’s a really good book called “Mistakes Were Made (But Not By Me): Why we Justify Foolish Beliefs, Bad Decisions, and Hurtful Acts” by Carol Tavris and Elliot Aronson. about this exact kind of behavior by people who are feeling uncomfortable levels of cognitive dissonance.
Once someone runs out of logical arguments to validate a belief, depending on what type of person they are, he/she does one of two things:
1) Reevaluate the opinion/belief in question, until it’s more in line with evidence.
Or
2) Hand-wavingly dismiss the evidence that is bothering them, then instead attack the person(s) presenting it via ad hominem.
The book is an excellent read. Whoever created that graphic is a textbook example.
I had to look up which schools wouldn’t let Susan wash their floors and I found that Thiru is a Woodlawn grad. Class of ’94, so he might well have known some of these people at a distance.
Also, glad he went the Ivy route, but being capable doesn’t mean someone is ethical or conscientious.
Not sure if this was asked already, but with all the evidence showing how much Yurick lied and withheld findings, will he be held accountable? What about the police? Anyone? Jay lying under oath…I mean, something?!
Urick definetly won’t suffer any repercussions. Prosecutors pretty much dont ever suffer any consequences for misconduct of this nature, period.
This is why prosecutorial misconduct is so endemic in the system. Prosecutors interested in career advancement know that getting convictions, especially high profile convictions, is the currency used.
Combine this with prosecutorial immunity from (for all intents and purposes) any and all consequences, they are completely incentivized to lie, cheat, and withhold as much as possible.
If they get caught mid-trial withholding exculpatory material, they begrudgingly turn it over, and assure the judge “Ok but NOW we really have no more Brady material. For realsies this time.” The absolute worst thing that can result is a future overturned conviction, but that’s gonna be many many years down the road. Long after whatever currency of career advancement earned from the conviction has long since been spent. Again, no skin off their back.
Urick is a slimeball, totally. But in this system where prosecutorial misconduct is so heavily incentivized, what else can we expect.
Congratulations, Susan. You guys have done some wonderful work.
Hi Susan,
This is my first ever question to your, but first I want to say how much I am in awe of all the work you all have. It is a simple question really on technicalities. When I read some documents that were presented in court, there are often mistakes in the spelling of names, e.g. Adrian M. Sayed on the AT&T documents at the top of this page, yet if I remember correctly Adnan’s age was falsified or incorrectly entered on documents that made him be judge under adult court. I would like your insight on how can the court accept documents with wrong information as proof, (making the spelling of his name irrelevant in that case), yet the mistake of his birthdate still prevails. What kind of mistakes would/could disqualify evidences, and why can’t the mistake of his birthdate cannot be? Hope this makes sense. Thank you.
Ok Susan, I can’t hold back anymore. you are absolutely RUINING the UNDISCLOSED podcast. Please stop reading off the paper you printed out hours before! You are not good at it!! If it wasn’t for you, zigs a 5 star podcast. Please let someone else read or take your place!
Ha, the joke’s on you, I never print out episode outlines!